Expand description
§rhabdomancer
“The road to exploitable bugs is paved with unexploitable bugs.”
– Mark Dowd
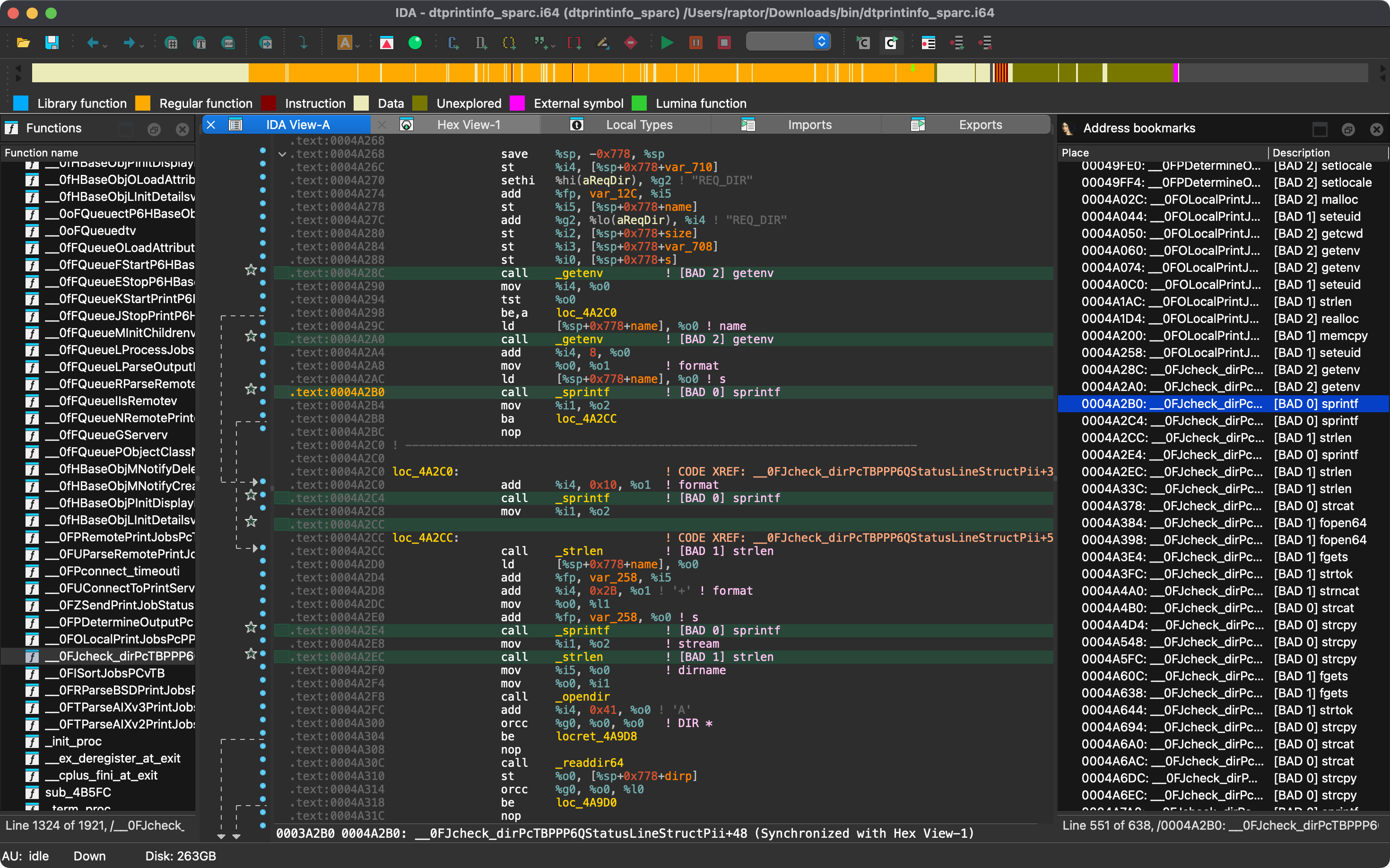
Rhabdomancer is a blazing fast IDA Pro headless plugin that locates calls to potentially insecure API functions in a binary file. Auditors can backtrace from these candidate points to find pathways allowing access to untrusted input.
§Features
- Blazing fast, headless user experience courtesy of IDA Pro 9.x and Binarly’s idalib Rust bindings.
- Support for C/C++ binary targets compiled for any architecture implemented by IDA Pro.
- Bad API function call locations are printed to stdout and marked in the IDB.
- Known bad API functions are grouped in tiers of badness to help prioritize the audit work.
- [BAD 0] High priority - Functions that are generally considered insecure.
- [BAD 1] Medium priority - Interesting functions that should be checked for insecure use cases.
- [BAD 2] Low priority - Code paths involving these functions should be carefully checked.
- The list of known bad API functions can be easily customized by editing
conf/rhabdomancer.toml.
§Blog posts
- https://hex-rays.com/blog/streamlining-vulnerability-research-idalib-rust-bindings
- https://hnsecurity.it/blog/streamlining-vulnerability-research-with-ida-pro-and-rust
§See also
- https://github.com/0xdea/ghidra-scripts/blob/main/Rhabdomancer.java
- https://docs.hex-rays.com/release-notes/9_0#headless-processing-with-idalib
- https://github.com/idalib-rs/idalib
- https://books.google.it/books/about/The_Art_of_Software_Security_Assessment.html
§Installing
The easiest way to get the latest release is via crates.io:
- Download, install, and configure IDA Pro (see https://hex-rays.com/ida-pro).
- Install LLVM/Clang (see https://rust-lang.github.io/rust-bindgen/requirements.html).
- On Linux/macOS, install as follows:On Windows, instead, use the following commands:
export IDADIR=/path/to/ida # if not set, the build script will check common locations cargo install rhabdomancer$env:LIBCLANG_PATH="\path\to\clang+llvm\bin" $env:PATH="\path\to\ida;$env:PATH" $env:IDADIR="\path\to\ida" # if not set, the build script will check common locations cargo install rhabdomancer
§Compiling
Alternatively, you can build from source:
- Download, install, and configure IDA Pro (see https://hex-rays.com/ida-pro).
- Install LLVM/Clang (see https://rust-lang.github.io/rust-bindgen/requirements.html).
- On Linux/macOS, compile as follows:On Windows, instead, use the following commands:
git clone --depth 1 https://github.com/0xdea/rhabdomancer cd rhabdomancer export IDADIR=/path/to/ida # if not set, the build script will check common locations cargo build --releasegit clone --depth 1 https://github.com/0xdea/rhabdomancer cd rhabdomancer $env:LIBCLANG_PATH="\path\to\clang+llvm\bin" $env:PATH="\path\to\ida;$env:PATH" $env:IDADIR="\path\to\ida" # if not set, the build script will check common locations cargo build --release
§Usage
- Make sure IDA Pro is properly configured with a valid license.
- Customize the list of known bad API functions in
conf/rhabdomancer.tomlif needed. You can override the default configuration file location by setting theRHABDOMANCER_CONFIGenvironment variable. - Run as follows:Any existing
rhabdomancer <binary_file>.i64IDB file will be updated; otherwise, a new IDB file will be created. - Open the resulting
.i64IDB file with IDA Pro. - Select
View>Open subviews>Bookmarks - Enjoy your results conveniently collected into an IDA Pro window.
[!NOTE] Rhabdomancer also adds comments at marked call locations.
§Compatibility
Only the latest IDA Pro release is officially supported, but older versions may work as well. The following table summarizes the latest compatible release for each IDA Pro version:
| IDA Pro version | Latest compatible release |
|---|---|
| v9.0.240925 | v0.2.4 |
| v9.0.241217 | v0.3.5 |
| v9.1.250226 | v0.6.2 |
| v9.2.250908 | v0.7.6 |
| v9.3.260213 | v0.8.1 |
| v9.3.260327 | v0.9.0 |
| v9.3.260421 | current release |
[!NOTE] Check the idalib documentation for additional information.
§Changelog
§TODO
- Enrich the known bad API function list (see https://github.com/0xdea/semgrep-rules).
- Consider converting
traverse_xrefsto an iterative walk to avoid potential stack overflows and infinite loops. - Consider broadening the scope of normalization in
normalize_nameto account for more cases. - Implement a basic ruleset in the style of VulFi and VulnFanatic.
Constants§
- PREFIX
- Prefix for bookmarks and comments
Functions§
- run
- Locate calls to potentially insecure API functions in the binary file at
filepath.





